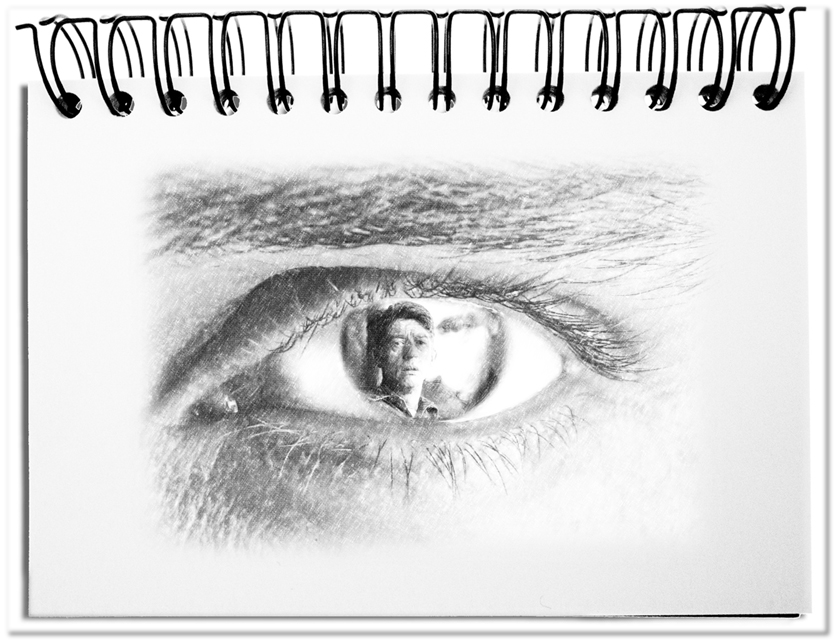
A utopia of total control was described again and again in books and movies. Think about 1984 by George Orwell, where Big Brother has control of the most private spheres of life. Or remember Fahrenheit 451 by Ray Bradbury, in which the possession or reading of books is legally forbidden and where the pervasiveness of the mass media in private life is well illustrated. These conceptions of the future that are shown in many science fiction stories provide an unattractive end state that was surely not developed at one go, but gradually. The required bases for such scenarios do not evolve from one day to the other. The whole begins completely innocently, by creating the controllability step by step.
The utopias provide only scrappy ideas, if at all, how these controls are created. The following steps show a possible scenario.
- Develop appealing offerings
Everything starts with the technical feasibility. New products and services provide attractive solutions that are becoming by and by affordable for most of the consumers. With the television the unidirectional connection of spectators began. Broadcasts were sent from one sender to many receivers. With the Internet we have the bi-directional connection between many senders and many receivers. In this case there is also data transmitted that does not serve the actual purpose (e.g. duration, frequency and the interests of the users). On this basis further applications are possible, like the navigation system, cashless payment or the electronic passport. These applications transfer more and more confidential data.
The users are thereby bound into the future control system, without being aware, how much they reveal about themselves. - Free use through advertisement and handing over data
For high prevalence more and more free or at least cheap offers are made that are “paid” with the supply of data. The users cannot determine, which data is getting exchanged with the data release or the regular update of the app.
For data fisher men, like the global secret services, it is a smart approach to develop an attractive software that supplies them directly with the appropriate information. - Creating laws and regulations
This procedure becomes legal by explicitly confirming the terms and conditions of an app by the users – without this confirmation one would not get the software. One suggests security to the citizens by limiting the duration of the data storing and, for example, the necessity for a judicial decision for using the data. This is raising the question, which spies would have ever been made responsible for their illegal bugging and monitoring actions. This makes the juridical question questionable.
The apparent rule of law is pure sham, as long as national borders and the nearly impossible control of their activities as well as the national self-interests provide the operators sufficient free space. - Facilitating exhaustive tracking
We weave today inadvertently a close meshed net of our behavior with the introduction of mobile offers, like the mobile phones, computers, navigation systems, location-dependent services and applications for detecting vehicles and packages as well as our individual browsing behavior. And everything can be found in the data storages of the Cloud. Calling a competitor of your employer by phone and the download of internal documents and the trip to this enterprise permit already nowadays unpleasant conclusions.
The infrastructure is already there. As soon as unscrupulous persons receive the access, we are in a still more terrible 1984. - Abolish alternative offers
In order to guarantee all this it is helpful that alternative behaviors are no longer available. With the conversion of payphones from coins to calling cards it is any more possible to phone, without storing the connection details. The abolishment of cash, as it is getting real in Scandinavia, makes it impossible to pay, without having the payment documented. The electronic passport guarantees that all border crossings can be evaluated.
As soon as those aspects of our everyday life are virtualized, everything is in the hand of those, who have control of this system.
This is nota re-narration of 1984, but a list of steps that lead to a pervasive monitor. With a close look, we will recognize that we let these steps already behind us in those regions of the world, where constant supply of electricity and information already exists. Occasional attempts to use these channels with appropriate filters for censorship leak out. This is not a classical end time scenario of conspiracy theoreticians, but our current reality. With the divulgence of governmental secrets by Snowdon, we had to learn that our fantasy is not big enough, in order to be able to imagine the current practices.
Bottom line: We already overhauled the utopia of George Orwell with today’s technical possibilities. The controllability of all people is technically possible today. If the scruples of those, who have the control, continue to disappear or control is taking over by a strong power, we will be in the position of Winston Smith – only with drastically expanded consequences.